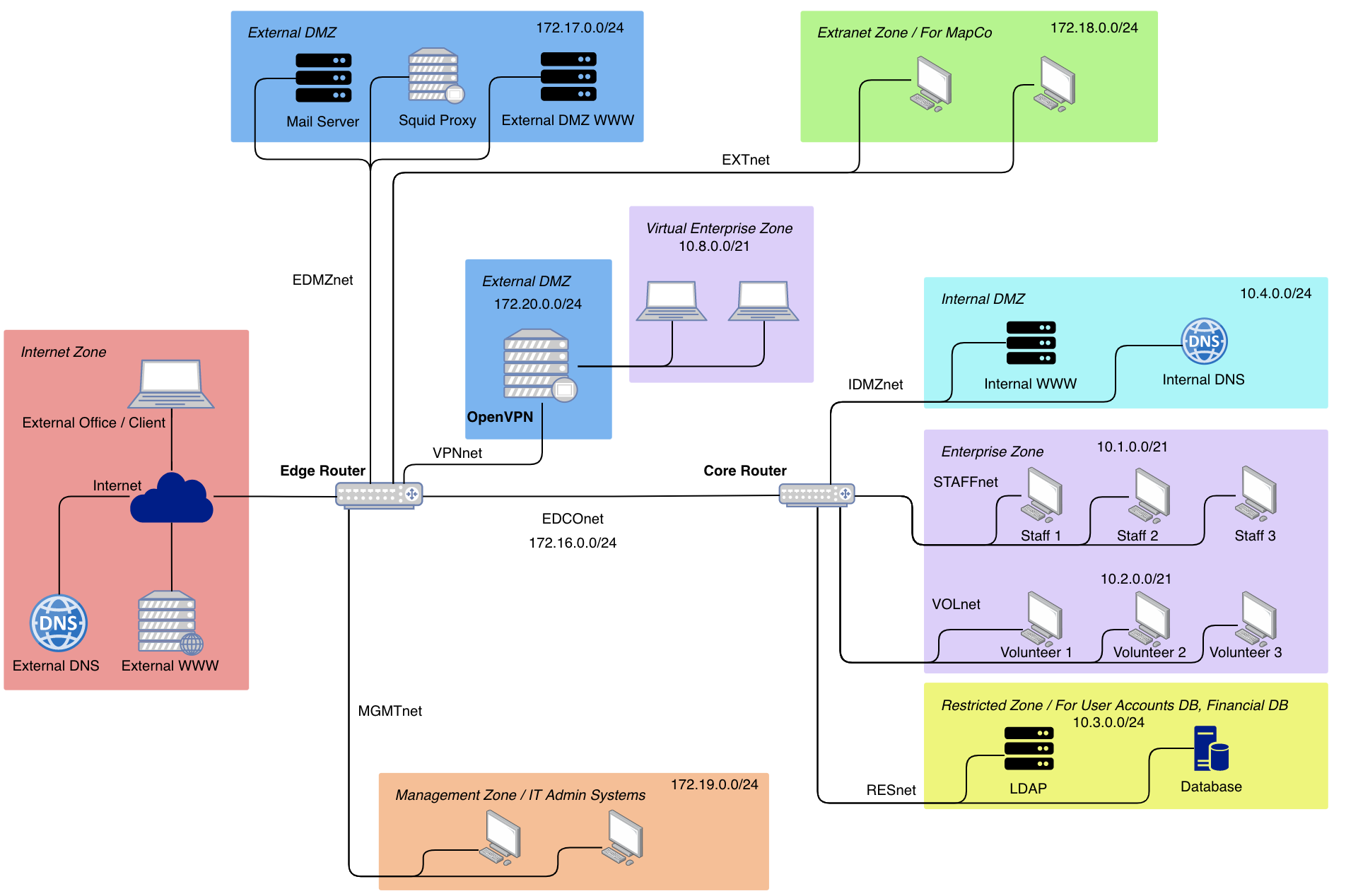
A scalable secure network infrastructure with defined credible zones of trust. It has automated iptables firewall rules deployment. It also has tested prevention firewall rules for TCP and UDP Flood attacks.
- 1. satisfy the case-sensitive file-naming requirements of the deliverable files.
- 2. define and implement credible zones of trust.
- 3. define and implement re-organised IP addressing.
- 4. define and implement filters between zones of trust.
- 5. partially verify that connectivity is achieved / prevented as appropriate between clients and services.
- 6. have hashes at the demonstration that match the hashes in the submission sandhashes.sha1 file (ie provide evidence that nothing significant has changed between the submission and the demonstration).
- 7. implement NAT / port-forwarding.
- 8. robustly verify that connectivity is achieved / prevented as appropriate between clients and services.
- 9. make a compelling case for your design.
- 10. implementation of one augmented feature.
- 10. implementation of two further significant, distinct, augmented features.
- 11. make a compelling case for your design.
- 12. demonstrate comprehensive mastery of all aspects of the the submission at all scales (detail through to overall concept).
- TCP SYN Flood Protection.
- UDP Flood Protection.
- Usage of OpenVPN to connect to internal network.
- Automation of host firewall rules deployment.
- Usage of Squid Proxy Server to access Internet from Enterprise Zone and Extranet Zone.
- Usage of Squid Proxy Server to block malicious websites.
- Blocking SSH access, allow SSH only from Management Zone.
- Blocking SSH access into root, allow SSH access only to admin account.
cd sand-pma-starterchmod +x /shared/hostrules.shlstart