If you have a self-hosted build server (e.g. Cloud VM), you may have security monitoring implemented on it. When you use GitHub Actions hosted-runner, you can use harden-runner to add security controls and monitoring to the build server (Ubuntu VM) on which GitHub Actions runs your workflows. Unlike traditional monitoring for Cloud VMs, harden-runner insights and policy are granular per job of a workflow.
First-of-its-kind patent-pending technology that automatically correlates outbound traffic with each step of a workflow.
-
Add
step-security/harden-runnerto your GitHub Actions workflow file as the first step.steps: - uses: step-security/harden-runner@14dc64f30986eaa2ad2dddcec073f5aab18e5a24 # v1 with: egress-policy: audit -
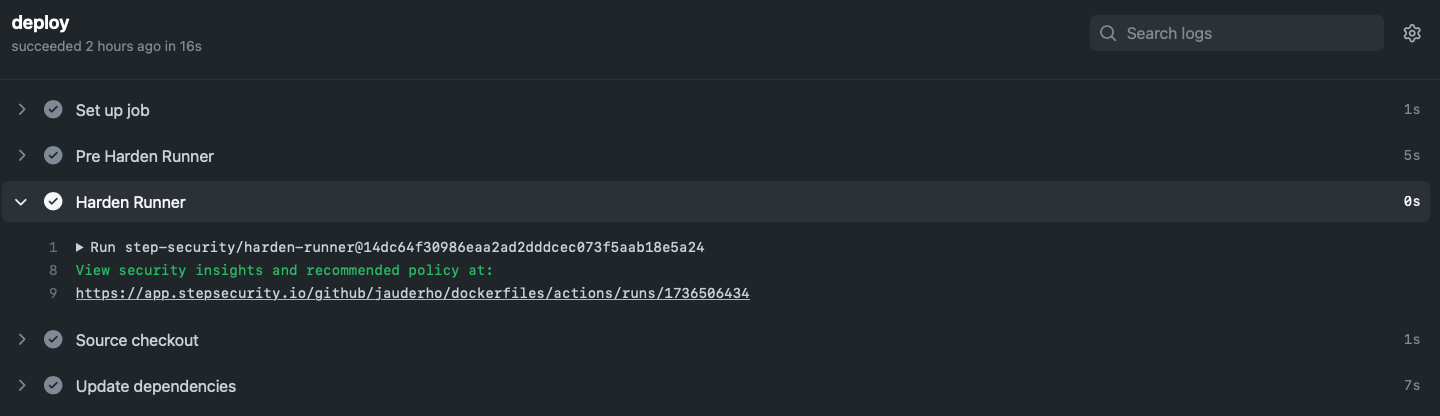
In the workflow logs, you will see a link to security insights and recommendations.
-
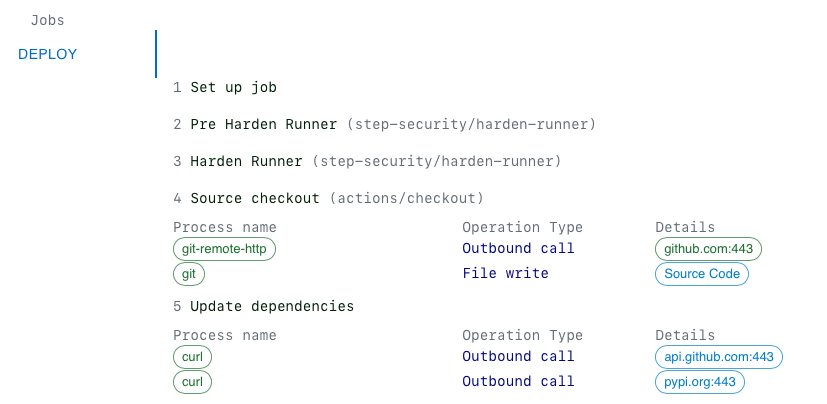
Click on the link (example link). You will see outbound traffic made by each step.
-
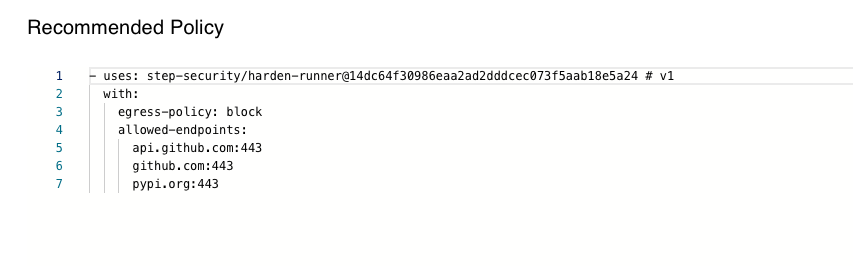
Add the recommended outbound endpoints to your workflow file, and only traffic to these endpoints will be allowed.
steps: - uses: step-security/harden-runner@14dc64f30986eaa2ad2dddcec073f5aab18e5a24 # v1 with: egress-policy: block allowed-endpoints: api.github.com:443 github.com:443 pypi.org:443
Hands-on tutorials to learn how harden-runner would have prevented past software supply chain attacks, such as the Codecov breach.
Workflows using harden-runner:
- https://github.com/nvm-sh/nvm/tree/master/.github/workflows (link to insights)
- https://github.com/microsoft/msquic/tree/main/.github/workflows (link to insights)
- https://github.com/Automattic/vip-go-mu-plugins/blob/master/.github/workflows/e2e.yml (link to insights)
- https://github.com/MTRNord/matrix-art/tree/main/.github/workflows (link to insights)
- https://github.com/jauderho/dockerfiles/blob/main/.github/workflows/age.yml (link to insights)
If you have questions, please use discussions.