在service mesh场景中,使用hessian-go作为序列化框架,需要解析dubbo请求body中的attachment(里面包含group)。因为attachment在body中方法参数字节的后面,所以需要先解析dubbo请求中的参数类型和参数值,然后才能去解析到attachemt。
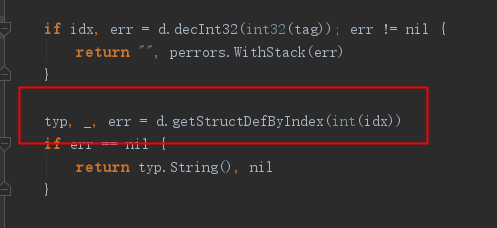
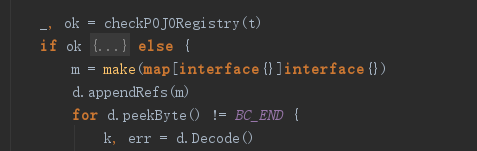
类似java的hessian序列化行为,如果反序列化类型找不到(比如是class类型),可以降级为hashmap(对应golang里面的map或者sync.Map). 这样参数解析完之后,也能解析到attachment。
bytes := []byte{
0xda, 0xbb, 0xc2, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x4c,
0x00, 0x00, 0x01, 0xfb, 0x05, 0x32, 0x2e, 0x36, 0x2e, 0x32, 0x30, 0x30, 0x63, 0x6f, 0x6d, 0x2e,
0x72, 0x61, 0x79, 0x63, 0x6c, 0x6f, 0x75, 0x64, 0x2e, 0x6e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x2e,
0x61, 0x70, 0x69, 0x2e, 0x73, 0x65, 0x72, 0x76, 0x69, 0x63, 0x65, 0x2e, 0x4e, 0x6f, 0x74, 0x69,
0x66, 0x79, 0x4a, 0x6f, 0x62, 0x52, 0x65, 0x71, 0x75, 0x65, 0x73, 0x74, 0x0e, 0x32, 0x2e, 0x30,
0x2e, 0x31, 0x2d, 0x76, 0x70, 0x63, 0x2d, 0x74, 0x65, 0x73, 0x74, 0x0d, 0x73, 0x74, 0x6f, 0x70,
0x4e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x4a, 0x6f, 0x62, 0x30, 0x2e, 0x4c, 0x63, 0x6f, 0x6d, 0x2f,
0x72, 0x61, 0x79, 0x63, 0x6c, 0x6f, 0x75, 0x64, 0x2f, 0x6e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x2f,
0x61, 0x70, 0x69, 0x2f, 0x64, 0x6f, 0x6d, 0x61, 0x69, 0x6e, 0x2f, 0x53, 0x74, 0x6f, 0x70, 0x4e,
0x6f, 0x74, 0x69, 0x66, 0x79, 0x4a, 0x6f, 0x62, 0x3b, 0x43, 0x30, 0x2c, 0x63, 0x6f, 0x6d, 0x2e,
0x72, 0x61, 0x79, 0x63, 0x6c, 0x6f, 0x75, 0x64, 0x2e, 0x6e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x2e,
0x61, 0x70, 0x69, 0x2e, 0x64, 0x6f, 0x6d, 0x61, 0x69, 0x6e, 0x2e, 0x53, 0x74, 0x6f, 0x70, 0x4e,
0x6f, 0x74, 0x69, 0x66, 0x79, 0x4a, 0x6f, 0x62, 0x98, 0x06, 0x73, 0x74, 0x61, 0x74, 0x75, 0x73,
0x06, 0x74, 0x6f, 0x70, 0x69, 0x63, 0x73, 0x04, 0x6e, 0x69, 0x63, 0x6b, 0x04, 0x74, 0x79, 0x70,
0x65, 0x0a, 0x73, 0x65, 0x73, 0x73, 0x69, 0x6f, 0x6e, 0x4b, 0x65, 0x79, 0x06, 0x61, 0x70, 0x70,
0x4b, 0x65, 0x79, 0x05, 0x61, 0x70, 0x70, 0x49, 0x64, 0x08, 0x74, 0x61, 0x6f, 0x62, 0x61, 0x6f,
0x49, 0x64, 0x60, 0x01, 0x31, 0x01, 0x31, 0x01, 0x31, 0x01, 0x31, 0x01, 0x31, 0x01, 0x31, 0x91,
0xe1, 0x48, 0x05, 0x61, 0x2e, 0x73, 0x2e, 0x75, 0x0a, 0x2f, 0x61, 0x75, 0x74, 0x68, 0x2f, 0x74,
0x65, 0x73, 0x74, 0x05, 0x61, 0x2e, 0x73, 0x2e, 0x74, 0x10, 0x35, 0x33, 0x35, 0x36, 0x32, 0x35,
0x38, 0x38, 0x39, 0x38, 0x37, 0x37, 0x31, 0x33, 0x31, 0x34, 0x05, 0x61, 0x2e, 0x73, 0x2e, 0x64,
0x10, 0x6b, 0x65, 0x66, 0x75, 0x2e, 0x6b, 0x75, 0x61, 0x69, 0x6d, 0x61, 0x69, 0x2e, 0x63, 0x6f,
0x6d, 0x04, 0x70, 0x61, 0x74, 0x68, 0x30, 0x30, 0x63, 0x6f, 0x6d, 0x2e, 0x72, 0x61, 0x79, 0x63,
0x6c, 0x6f, 0x75, 0x64, 0x2e, 0x6e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x2e, 0x61, 0x70, 0x69, 0x2e,
0x73, 0x65, 0x72, 0x76, 0x69, 0x63, 0x65, 0x2e, 0x4e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x4a, 0x6f,
0x62, 0x52, 0x65, 0x71, 0x75, 0x65, 0x73, 0x74, 0x10, 0x64, 0x75, 0x62, 0x62, 0x6f, 0x41, 0x70,
0x70, 0x6c, 0x69, 0x63, 0x61, 0x74, 0x69, 0x6f, 0x6e, 0x14, 0x63, 0x6f, 0x6d, 0x2d, 0x72, 0x61,
0x79, 0x63, 0x6c, 0x6f, 0x75, 0x64, 0x2d, 0x61, 0x64, 0x6d, 0x69, 0x6e, 0x2d, 0x78, 0x09, 0x69,
0x6e, 0x74, 0x65, 0x72, 0x66, 0x61, 0x63, 0x65, 0x30, 0x30, 0x63, 0x6f, 0x6d, 0x2e, 0x72, 0x61,
0x79, 0x63, 0x6c, 0x6f, 0x75, 0x64, 0x2e, 0x6e, 0x6f, 0x74, 0x69, 0x66, 0x79, 0x2e, 0x61, 0x70,
0x69, 0x2e, 0x73, 0x65, 0x72, 0x76, 0x69, 0x63, 0x65, 0x2e, 0x4e, 0x6f, 0x74, 0x69, 0x66, 0x79,
0x4a, 0x6f, 0x62, 0x52, 0x65, 0x71, 0x75, 0x65, 0x73, 0x74, 0x07, 0x76, 0x65, 0x72, 0x73, 0x69,
0x6f, 0x6e, 0x0e, 0x32, 0x2e, 0x30, 0x2e, 0x31, 0x2d, 0x76, 0x70, 0x63, 0x2d, 0x74, 0x65, 0x73,
0x74, 0x07, 0x74, 0x69, 0x6d, 0x65, 0x6f, 0x75, 0x74, 0x04, 0x35, 0x30, 0x30, 0x30, 0x5a,
}